Is ethereum secure?
If you’re playing with the idea of trading cryptocurrency and ethereum, you may have asked yourself the question: “But is ethereum actually safe?”. You can learn more about that here.
First, there are three things that are good to know:
- Ethereum, and cryptocurrencies in general are built on technology which theoretically should strengthen security when it comes to money.
- Cryptocurrency is still a very new concept, and many countries still don’t allow the use of ethereum and other cryptocurrencies as a payment method yet.
- Ethereum and cryptocurrencies are unregulated assets which means that there are risks connected to buying and selling them.
That can be distilled down into three topics, you need to get acquainted with to find out whether or not ethereum is safe:
- What makes ethereum a secure currency?
- What countries allow the use of ethereum?
- Why is buying and selling ethereum connected to risks?
What makes ethereum a secure currency?
The blockchain technology, which ethereum is built upon, is what should strengthen security. In this context the technology utilises three important features:
Encryption, immutability, and consensus.
If you’re not already familiar with blockchain, you can learn more about the technology here .
Encryption
Central for blockchains are that they store transaction information in large blocks of data. So, to exemplify, if you were to purchase a litre of milk from Anna with bitcoin, it would appear in the data blocks in the bitcoin-blockchain.The information stored in a blockchain is also protected against hacker attacks and similar attempts to infiltrate the system.
Any transaction on the blockchain is encrypted, so when you purchased milk from Anna, it was registered on the blockchain with an encrypted code.
For example: “You” + “Anna”
251E0CCC225C3DD5E0B30A9905FAC57805EDDE786B665A6EA2429D2357870581
This means that no one can see what’s actually behind the encryption. On the other hand, everyone can ascertain that a transaction has happened between “You” and “Anna”. In reality, the names are also anonymous.
Immutable
The technology also prevents changes in information added to the blockchain. This means that cyber criminals for example can’t go into the system and change or manipulate information. This means that the blockchain is ‘immutable’.
In theory, this should make sure that no one can ever say that your purchase of 1 litre of milk from Anna never happened. This could be relevant in the event of Anna alleging that she hasn’t received payment from you yet, and she would therefore want the amount transferred again.
Here, it’s clearly visible on the blockchain that the transaction actually took place.
Consensus
A last common characteristic of blockchains to make them more secure is the way in which new blocks of data are being validated. Because what if a hacker, Hans, got access to the blockchain and simply added a transaction, where Hans should now receive 10 ethereum from Anna?
If Hans were able to do so, it would appear as if Anna should transfer 10 ethereum to Hans.
And when Anna gets the bill, she may not even think about it if she were a milk wholesaler.
But that can’t happen. Because before any new transaction can be added to a blockchain it would first require that everyone in the blockchain network validates the transaction. This is also called a consensus mechanism.
So when one person validates the transaction, it’s added to their version of the blockchain. That version will then be forwarded in the network, where the next person would have to validate the transaction in their version of the blockchain.
The idea of a blockchain rests on the fact that the network is honest. Because sooner or later, an honest person in the network will be able to tell that the transaction between Anna and Hans is faulty, and they would then remove the transaction from their version of the blockchain. That version is then forwarded further in the network, and provided that the network is honest, they would prioritise forwarding the honest version instead of the faulty version that Hans sent out.
So in theory, it’s possible for Hans to trick the network – all it takes is that 51% of the network is dishonest and would prioritise Hans’ version of the blockchain.
But here, it needs to be clear that 1 participant in the network doesn’t equal 1 person, but depends more on computer power. It requires a certain amount of computing power to validate transactions, and one computer could be able to contribute 10 times as much as compared to other computers.
In that way, one person could be responsible for 2% of the network’s computing power, while another person is responsible for 0,1%. Theoretically speaking, a single person could then be responsible for more than 51% of the network’s computing power and trick the whole system single handedly. In practice, that’s quite difficult, as that amount of computing power would be very expensive.
What countries allow ethereum as a payment method?
Ethereum can be an uncertain currency to carry, if you plan to use it as a payment method .
Not all countries accept ethereum and other cryptocurrencies as a legal payment method.
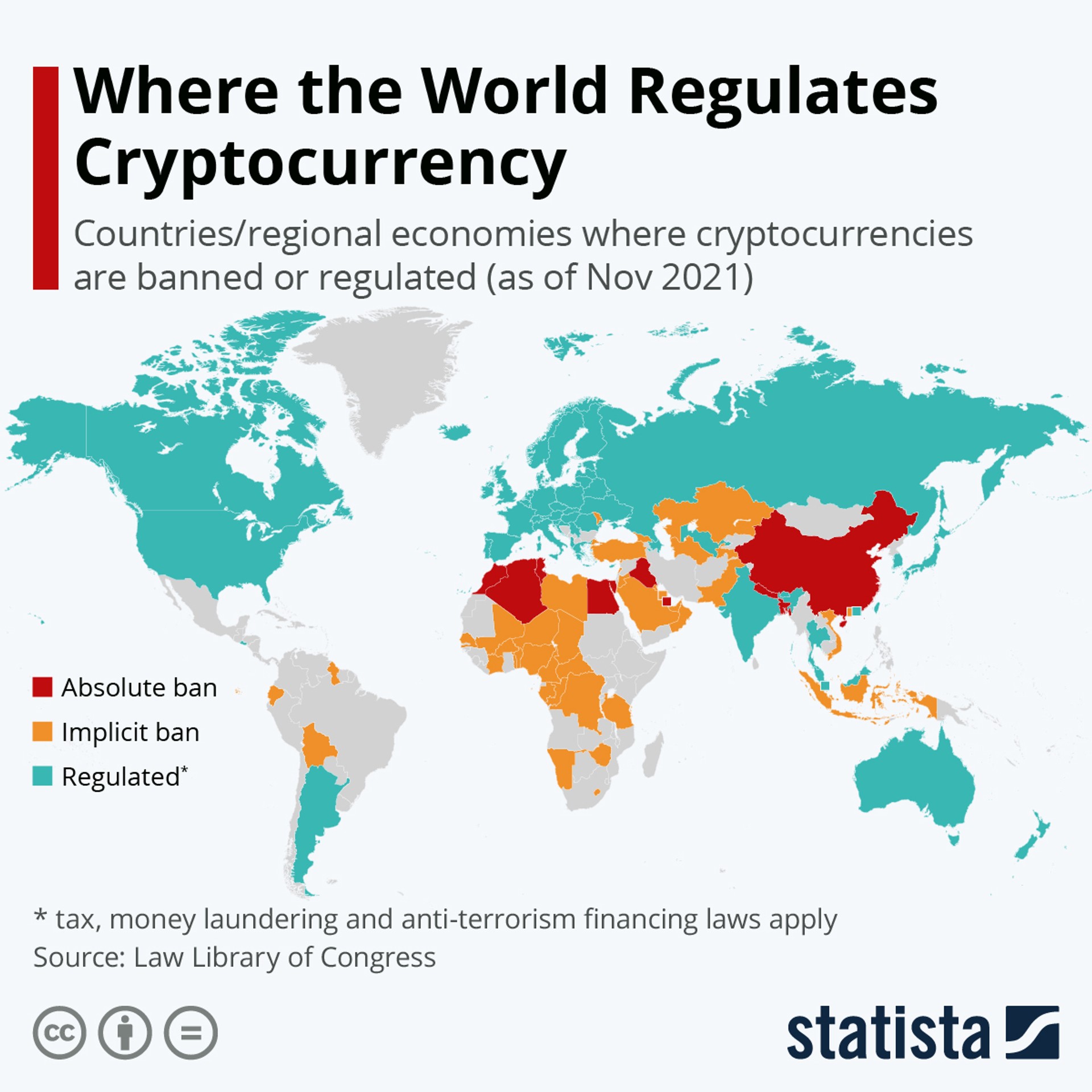
On the map from Statista you can see which countries who:
- regulates crypto (blue)
- implicitly bans crypto (yellow)
- absolutely bans crypto (red)
See here, where you can pay with ethereum.
What makes ethereum an uncertain investment?
When you trade ethereum there’s a risk that you could lose some or the entirety of your holding. Ethereum and cryptocurrencies in general are unregulated which means that there are no central authorities to protect consumers.
If you have money in a bank, and the bank goes bankrupt, your money is protected by a central authority: In Denmark, that authority is Garantiformuen. Garantiformuen covers deposits on amounts corresponding to 100,000 EUR per depositor and securities on up to 20,000 EUR per investor.
But if you lose your ethereum following a cryptoplatform going bankrupt, you’re not protected by any authorities.
That is one of the reasons why ethereum is an uncertain investment.
Besides that, ethereum is a very volatile asset . This means that prices can rise and fall very quickly. The more volatile an investment is, the more uncertain it is. The same goes for all types of assets. For example, if you were considering buying a house, you would be more careful with your purchase if you knew that the price of the house potentially could lose up to 100% of its value from one day to the next. At the same time, there’s also a risk that the house could be worth 10 times the price the next day.
That’s kind of how ethereum works. You should consider whether ethereum fits your readiness to take risks.
Cryptocurrencies can rise and fall
When you trade cryptocurrencies, you need to be aware that it carries a large risk. The value of your cryptocurrency can both rise and fall, and you can risk losing the entire amount you’ve invested in cryptocurrencies.
Cryptocurrency trading is done through Lunar Block. Lunar Block is not regulated by the Danish Financial Supervisory Authority (Finanstilsynet). That means you won’t have the same protection as when trading e.g. stocks or other regulated assets.
We do not counsel
We do not advise on currencies and do not make recommendations for either buying or selling. We can provide factual information about the different currencies, but past price developments are not an indication of future developments.
No information from Lunar Block should therefore be considered as recommendations and all decisions are up to you alone.
Last updated April 18, 2023. We’ve collected general information. Please note, that there may be specific circumstances that you and your business need to be aware of.
You might also like...
Where can I pay with solana?
Cryptocurrency is becoming so widespread and acknowledged abroad that you can use the currency just like regular payment methods on some...
How do you buy solana as regular stocks?
Because solana (SOL) is a currency, and not a business, you can’t actually invest directly in solana like it’s a stock.
Are cryptocurrencies a good investment?
Cryptocurrencies can be a great addition to your portfolio - if you’re willing to run the risk. Cryptocurrencies are “high risk - high...
What is bitcoin?
Bitcoin is a digital currency, or cryptocurrency, as it’s also called. Bitcoin is the first and largest cryptocurrency measured on market...